
IT Solutions
FIPS Validated File Transfer Products
What are FIPS?
The acronym FIPS stands for Federal Information Processing Standards. These are standards required by the United States Federal Government for use in information processing activities and systems employed by non-military government agencies and government contractors. A FIPS may be issued simply to establish a standard way of processing data where an industry standard does not exist. Such is the case with FIPS 10-4 for country or region codes and FIPS 5-2 for US state and county codes. In other cases, they detail specific methodologies intended to assure security best practices and interoperability as is the case with FIPS 140-2. FIPS standard specifications are sometimes based on technical industry standards such as those from the American National Standards Institute (ANSI) or the Institute of Electrical and Electronics Engineers (IEEE).
FIPS 140-2: A Cryptographic Module Federal Government Standard
The U.S. Federal Information Processing Standards (FIPS) 140-2 is part of the 140 publication series issued by the National Insttitute of Stantards and Technology (NIST). The 140 series is meant to define requirements for cryptographic modules for hardware and software components. The requirements are extensive and cover not only the modules themselves but also thier documentation.
It is important that agencies implementing FIPS 140-2 'compliant' modules confirm that they are, in fact, covered by an existing validation certificate. Vendors often claim compliance without having gone through the rigors of validation. These validation certificates specify the exact module, product and hardware or software version numbers validated under the Cryptographic Module Validation Program (CMVP) operated jointly by NIST and the Communications Security Establishment (CSE) of the Canadian Government.
FIPS 140-2 was published in 2001 by the U.S. National Institute of Standards and Technology (NIST), a non-regulatory agency of the U.S. Department of Commerce. NIST works to establish various standards that the U.S. military and various government agencies must abide by. Vendors, contractors, and any organization working with government or military must comply with FIPS as well. The Canadian government also has policies requiring FIPS-validated software, and it cooperates with NIST in establishing FIPS standards.
FIPS 140-2 Requirements
In cases where a high level of security is required, a FIPS-validated data-transmitting application must both use algorithms and hash functions approved by FIPS 140-2 and be validated by the Cryptographic Module Validation Program (CMVP). The CMVP is a testing process under the supervision of the U.S. NIST and the Communications Security Establishment (or CSE, which serves as NIST’s validation functions in Canada).
A FIPS-validated solution must use cryptographic algorithms and hash functions approved by FIPS. The following are three examples of such approved algorithms:
- AES (Advanced Encryption Standard) is a new algorithm adopted by NIST in 2001. It is stronger than Triple DES (Data Encryption Standard) when using greater key strength.
- Triple DES a variant of IBM’s 56-bit DES encryption that uses three keys for a total of 168-bit strength. Triple DES was approved by NIST for use in 1999.
- HMAC SHA-1 is a cryptographic hash function designed by the National Security Agency (NSA). It authenticates messages and is deployed in combination with a secret key.
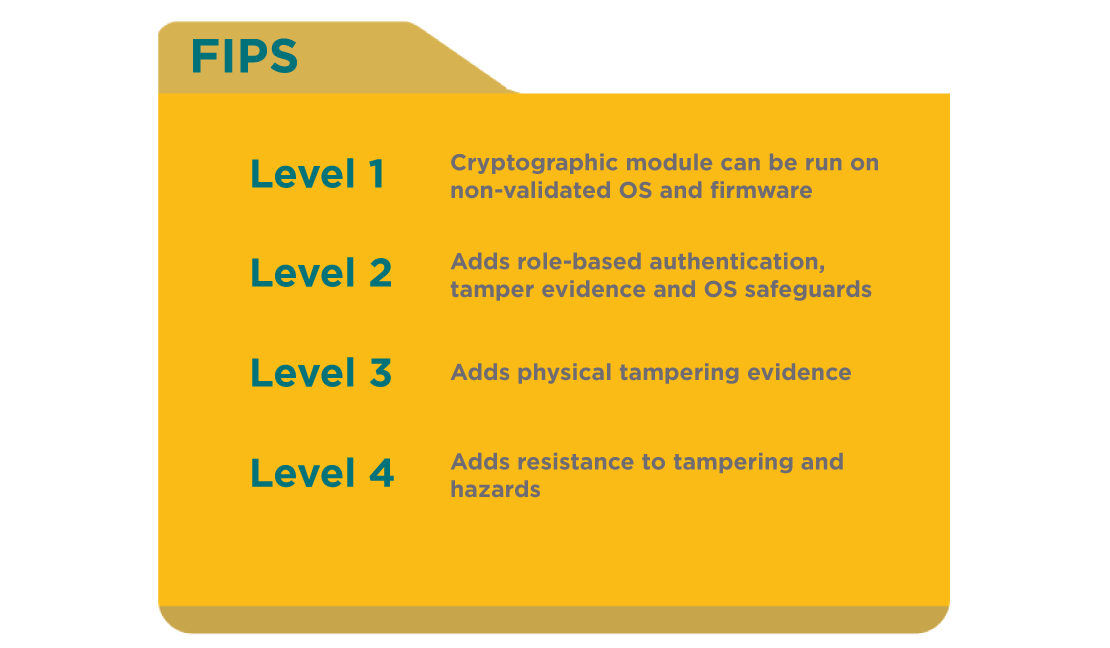
FIPS 140-2 Security Levels
While FIPS 140-2 does not specify a required level of security for any specific software or hardware application, it does denote four levels of security as follows:
- Level 1 - basically sates that all components of cryptographic modules be " production-grade" and have enough security as to be capable of running on non-validated OS and firmware
- Level 2 - adds requirements for physical tamper-evidence, role based-authentication and OS safeguards
- Level 3 - adds requirements that the design be tamper-resistant (that the supplier has taken steps to make it difficult for attackers to gain access to sensitive information, identity-based authentication and measures for physical or logical separation of critical security interfaces
- Leve 4 - adds stringent physical security requirements to mitigate the risk of tampering and environmental hazards compromising the security of sensitive data.
FIPS Validated vs FIPS Compliant
Only NIST can certify that a product adheres to the FIPS specification and they do so through an exhaustive testing process that results in a 'FIPS Validation'. Many file transfer solutions claim to be “FIPS compliant”, but this only means they believe they comply with the standard. Creating FIPS-validated solutions not only involves using approved algorithms, but also providing NIST with software that is well documented, well engineered, and tested, and also is easily testable in ways that help move the validation process forward in a timely way.
NIST not only tests the software operationally, but also checks for security flaws, such as the incorrect use and disposal of keys in memory, and the predictability of “random” number generation. It also verifies the presence of module self-integrity checks (which prevent tampering), and checks for possible back doors and hard-coded keys. It is important to note that with file transfer software, both client and server applications must be validated. Other systems and processes involved in the software’s operation must be validated as well.
FIPS Validated Products
WS_FTP Server - FIPS certificate 1747
WS_FTP Server’s encryption transfer, integrity checking (FTP, HTTP, and HTTPS), HTTPS transport, FTP commands, and data-stream encryption are all validated under the FIPS-validated module. These all use AES encryption for transaction privacy and HMAC SHA 1 for data-integrity checking. WS_FTP’s solution is validated by FIPS certificate 1747, with specific protocols validated by 613, 668, 701, and 352 (under the OSSI’s Open SSL).
MOVEit - FIPS 140-2 Certificate 1363
MOVEit Transfer and MOVEit Automation applications both use FIPS-validated AES and SHA-1 for encryption. MOVEit’s validation falls under 140-2 certificate 310, with specific protocols validated by certificates 30 and 124. Together with a FIPS-validated Windows operating system, MOVEit Transfer also uses a FIPS-validated encryption for HTTPS transport, FTP commands, and data-stream encryption. MOVEit Automation also uses FIPS-validated encryption for encryption of configuration files, and for HTTP, HTTPS, and FTP integrity checking. With a FIPS-validated Windows operating system, MOVEit Automation is also FIPS-validated for HTTPS transport encryption, FTP command, and data stream encryption.
Download the PDF
