File Transfer & Information Security Blog
Featured Articles

-
CISA Certification: What You Need to Know
A certified information systems auditor (CISA) carries a specialty certification that indicates a mastery of IT security in the realms of governance, risk and compliance. And although it's not required, CISA certification is a big boost for the IT department in some...
-
Does your FTP server provide regulatory compliance?
Requirements for protecting data being transferred internally or externally vary, but there are commonalities across industry regulations, national and state laws, and security specs.
-
Top 5 Life Hacks for IT Pros
Life hacks have been an online sensation for years. From separating a yolk from egg whites with a plastic bottle to creating a simple iPhone speaker with just some tacks and an empty toilet paper roll, life hacks have become a way of life for many of us. It seems that...
-
8 Easy Ways to Celebrate SysAdmin Day
Jeff Loeb | | IT Insights
Today marks the 16th annual System Administrator Appreciation Day, also known as SysAdmin Day. This is a day where everyone should take a moment to thank their SysAdmins (and pretty much everyone else on their IT team) for their hard work. IT pros like SysAdmins get far...
-
How to Simplify a Compliance Audit
With an alarming number of security breaches and data loss this past year, maintaining compliance with industry regulations is a top concern for IT pros and senior leadership. So why are IT departments leaving compliance and security processes to chance? (Particularly...
-
Top 6 Requirements for Choosing File Transfer Technology
Life throws a lot of really tough decisions at us, but choosing a file transfer technology shouldn’t be one of them. File transfer expert Don Jones offers a checklist of requirements, and today I'd like to share his top 6 that company should consider:
-
Five Ways Dropbox Will Get You Fired
The popularity of consumer file-sync-and-share solutions such as Dropbox continues to grow, as consumers appreciate the ease with which they’re able to transfer large files, such as photos and videos, to family and friends. While beneficial to consumers, these...
-
Managed File Transfer vs. SOA: Round 2
Part 2: The convergence of Managed File Transfer-as-a-Service and SOA for multi-enterprise integrations
-
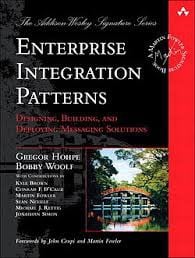
Managed File Transfer vs. SOA
File transfer has been a common and serviceable way to exchange information among computer systems since the dawn of digital time. Even today, despite the growing use of transactional integration technologies like service-oriented architecture (SOA) and enterprise...
-
4 Reasons Why High Availability is a Must-Have
On the surface, it would seem that high availability (HA) and disaster recovery (DR) for file transfer processes would have always been a top priority. While true for some organizations, not everyone has considered it an essential component. It seems that’s changing, as...
-
5 Key Considerations When Using PGP Encryption in File Transfer
Steve Staden | | Security
When you’re moving files containing sensitive information, you want to make sure it’s encrypted and not available to prying eyes, whether the data is at rest or in motion. A proven way to protect files before, during, and after transfer is via PGP file encryption. In...
-
Protect Your Data and Integrate Secure File Transfer with Antivirus
Every day, files are exchanged between your systems, employees, and business partners on a global scale - but are they integrated with an antivirus solution? It’s no secret that with each file transfer, your organization faces potential exposure to viruses, worms, Trojan...
-
The City of Guelph Embraces Managed File Transfer
To better understand Managed File Transfer (MFT), it’s useful to review actual use cases. I think of the City of Guelph as a prime example of what prompts organizations to migrate from simple consumer-grade Enterprise File Sync and Share (EFSS) for file transfer to more...
-
Four Reasons Every Business Needs a Managed File Transfer Solution
As an IT analyst firm, we query companies large and small on a range of issues. One of the areas of risk we consistently see is around the transfer of files associated with business processes. To understand why these risks exist, we need to explore the difference between...
-
Encryption: Transport versus File
This morning I was asked if I recommended using transport encryption or file encryption to protect company files and data.
-
Managed File Transfer & WAN Acceleration
Many customers today expect ‘WAN acceleration’ technology (sometimes referred to as WAN Optimization) as part of their MFT vendor’s solution offering. In general this is a useful addition to the MFT feature set, and can certainly reduce file transfer times in a wide variety...
-
Why do I need Managed File Transfer? Isn’t FTP enough?
Aaron Kelly | | Security
The Internet’s venerable File Transfer Protocol (FTP) is usually supported by Managed File Transfer (MFT) systems, which can typically use FTP as one of the ways in which data is physically moved from place to place. However, MFT essentially wraps a significant...