If 2017 was the year of the ransomware attack, then 2018, insofar as it can be defined by malware, was the year of cryptojacking.
In early 2018, the cryptocurrency market hit unprecedented levels, leading to a boom in cryptocurrency mining, both legal and illicit. And now, while the dizzying highs of cryptocurrency prices and the bitcoin bubble (is it fair to call it a bubble now?) have crashed back down to reality, criminals are still making a killing by using cryptojacking to mine lesser-known alt-coins such as Monero.
In this post, we’ll explain the basics of what cryptojacking is, and how you can detect and block it on your network.
What is Cryptojacking?
Cryptojacking works by—you guessed it—hijacking other people's processing power and using it to mine cryptocurrencies. This is typically achieved with scripts that run behind the scenes on websites, though it's also possible to hijack machines and servers to run full-blown cryptocurrency mining software, which is either installed by malware or by rogue employees.
As Peter from Spiceworks put it, "Cryptojacking is a bit like someone else taking out your car and earning money with it on Uber without you knowing, collecting the profits behind your back, and hoping you don't notice."
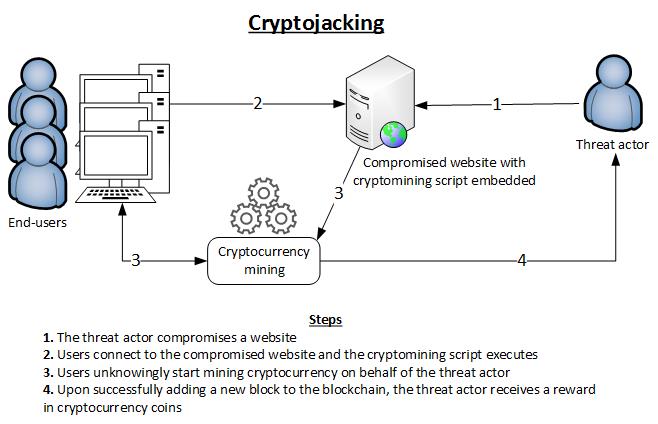 |
| Image via ENISA |
Or, to put it another way, imagine a stranger is using your house when you're off at work, using the water, the electricity, the heat— it's a bit like that.
For hackers, the benefit is obvious: they can mine cryptocurrencies without paying the astronomical electric bills that generally come with such activity.
Now, I know what you're thinking: cryptomining on a CPU is incredibly wasteful. It's harmful to your hardware and just flat-out inefficient in terms of energy used vs. currency mined. So unless you have a powerful GPU, you should be safe from cryptojacking, right? Not quite. For cryptojackers, those downsides are moot points. Think about it—if you've got thousands of users running your script to hijack their computing power and electricity to do the job, cryptojacking is essentially free money, and that's very tempting for the morally bankrupt. Not to mention that Monero mining is much less resource-intensive than traditional Bitcoin mining.
How Much of a Threat is Cryptojacking?
But beyond being the newest cybersecurity buzzword, is cryptojacking really a threat? Short answer: Yes.
Recent reports have shown exactly how profitable cryptomining can be. In one instance, hackers created a botnet of cryptominers, dubbed "Smominru" by security researchers, that controls over 520,000 machines—that's nearly as large as the Mirai botnet that nearly broke the internet in 2016—and amassed nearly $2.3 million in cryptocurrency. That's a hefty profit, and it creates strong incentive for others to follow. And it seems that many have...
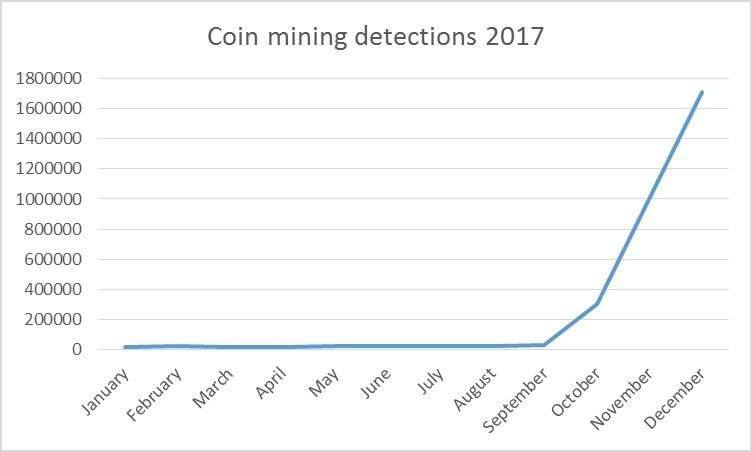 |
| Image via Symantec |
And news reports are backing these claims up. Cryptojacking has been all over the news in 2018: Cryptojacking has surged in popularity in recent years—it grew by a factor of 8500% in 2017, and has surpassed ransomware in popularity, according
to
research from Symantec. In fact, in their recent State of Malware report, researchers at
Headlines back this claim up. In recent months, cryptojacking has been all over the news, from run-of-the-mill browser scripts to industrial SCADA control systems infected with crypto mining software. In one extraordinary case, a Russian scientist was arrested for cryptomining on a super computer at a nuclear lab.
And the cryptojacking epidemic doesn't just cost victims resources, it can actually destroy their equipment. One type of Android malware, called Loapi, mines cryptocurrency so intensely that it can actually cause physical harm to the device that it runs on.
With all this in mind, I'd say it's safe to say that the cryptojacking threat is real, and it's not going anywhere. So, how do you secure your network from cryptojackers who want to burn your resources—whether they're hackers running in-browser mining scripts, or rogue employees looking to take advantage of powerful computing systems?
Basic Steps: Patch Your Systems
This is a fundamental first step to protecting yourself from thousands of attack vectors—and something you should be doing anyway—but it's worth repeating: always keep your machines patched and up-to-date. ESPECIALLY if the patch notes mention any kind of security vulnerability.
Staying up to date on your patches and security updates is an easy way to keep trojans carrying cryptominers off of your network. When it comes to cryptojacking, every day is Patch Tuesday. Out-of-date applications and operating systems are a favorite attack vector for bad guys, and they're one that you can easily close, so just do it. Case in point: Smominru, the 500k strong cryptomining botnet mentioned above, uses long-patched vulnerabilities such as the EternalBlue exploit and EsteemAudit to take over Windows machines. By patching your machines and removing those attack vectors, you decrease the chance for cryptominers to get access to your resources.
Block Your Attack Vectors
While patching is a critical step, even a fully patched system can be vulnerable if a user visits the wrong site, or installs the wrong app, and that's why it's important to take a multifaceted approach to blocking cryptojackers—especially those that run in-browser.
The most straightforward solution to this problem would be to block JavaScript from running in browsers on your network, but that would make for a pretty miserable internet experience. I can only imagine the number of tickets and user complaints. So, in most cases, it's probably better to take a more nuanced approach. This can be done by blacklisting domains, or by using software or plugins to do it for you.
Many AV solutions, such as BitDefender, Avast, and MalwareBytes automatically block mining sites such as CoinHive miner's JavaScript from accessing their domain and IP. These solutions should also be capable of detecting and blocking exploits like EternalBlue, which can get you in a whole lot more trouble than simple cryptojacking. If you don't already have a security system like this in place, we strongly advice that you get one.
For free solutions, NoCoin, Coin-Hive Blocker, and MineBlock are all solid options for blacklisting cryptomining domains. Or you could use an ad blocker likeuBlock Origin (my personal choice). Alternatively, you can create a blacklist of your own, though it can be difficult to keep up-to-date.
Monitor for Abnormal GPU and CPU Usage
While the methods outlined above will certainly keep you better protected than doing nothing, the truth is that there's no silver bullet for keeping cryptominers off of your network. There is, however, one sure thing. You can monitor for, and identify misbehaving machines, and then address the issue from there.
Regardless of the method used, mining cryptocurrency is going to be a major resource hog, which should make the machines doing it stand out. This is especially true in off-business hours when most machines will be less active, but those with cryptominers installed will continue using resources at a high rate.
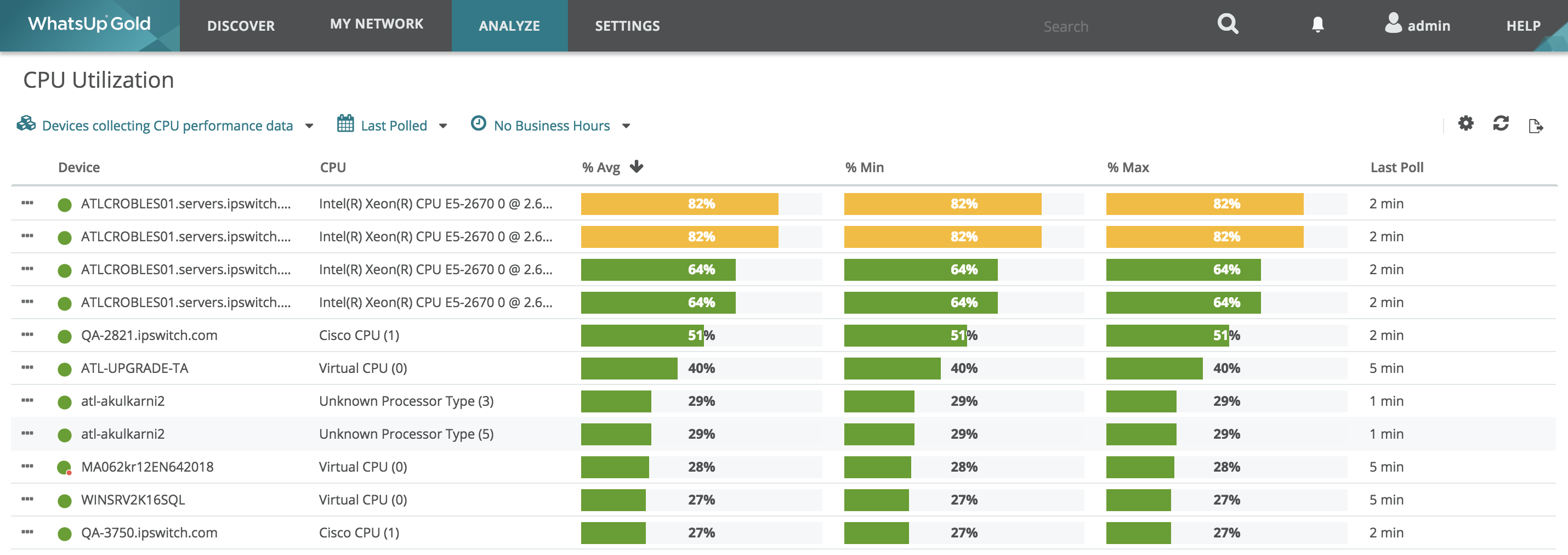 With a modern network monitoring tool, like WhatsUp Gold, you can easily monitor for CPU spikes and set up alerts for when CPU usage exceeds 90% (or any other threshold you want) on machines that don't regularly perform CPU-intensive tasks. This is a simple way to
keep track of your machines and find out if there's anything strange going
on.
With a modern network monitoring tool, like WhatsUp Gold, you can easily monitor for CPU spikes and set up alerts for when CPU usage exceeds 90% (or any other threshold you want) on machines that don't regularly perform CPU-intensive tasks. This is a simple way to
keep track of your machines and find out if there's anything strange going
on.
In WhatsUp Gold, monitoring for CPU spikes is a preset configuration, and blackout policies can be used to limit monitoring to off-business hours if so desired. Likewise, setting up alerts for spikes in CPU usage is easy to configure. You can try it yourself with a free trial, available here.
At any rate, it doesn't look like the crypto-mining frenzy is coming to an end anytime soon, so stay protected with the tips above, and keep current with your patches and blacklists. If you have any other techniques for keeping cryptominers off of your networks, please feel free to share them in the comments.
